DNS Domain Name Server Notes
DNS Domain Name Server Notes
DNS Domain Name Server: Note
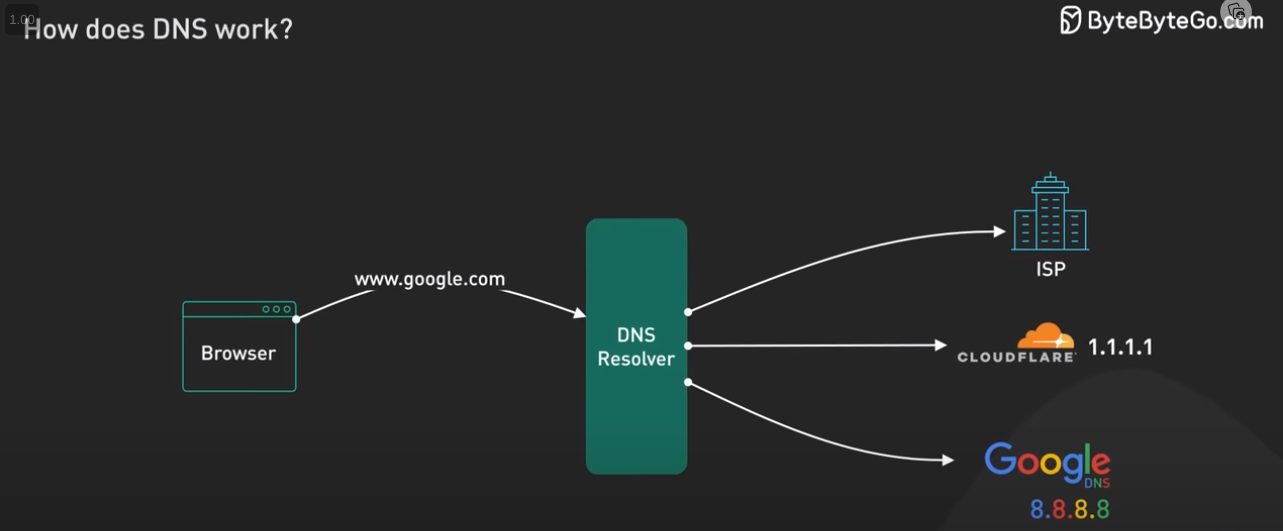
10,000 FT View
DNS Resolver Providers
What is Software that makes DNS Server work
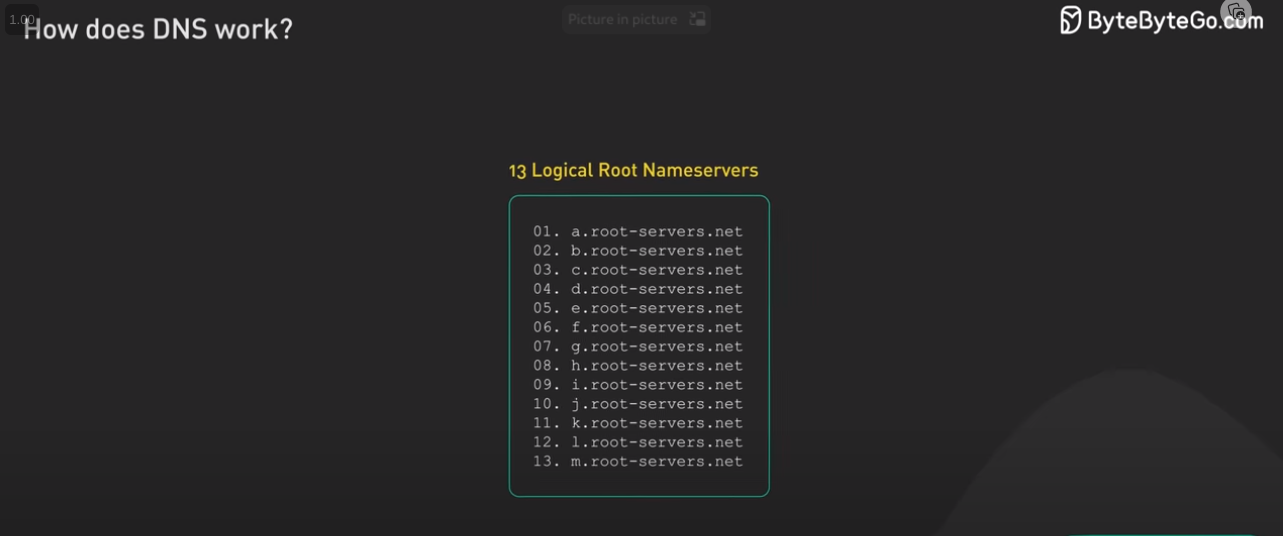
Why only 13 root DNS servers ?
- A common misconception is that there are only 13 root servers in the world.
- In reality, there are many more, but still only 13 IP addresses used to query the different root server networks.
- Each has associated with it an IP address (and shortly some will have more than one as IPv6 is further rolled out)
- There are 13 logical root name servers specified, with logical names in the form letter.root-servers.net, where the letter ranges from a to m.
- which specifies a maximum packet size of 512 bytes when using the User Datagram Protocol (UDP).
- Technically, however, fourteen name servers fit into an IPv4 packet.
- The addition of IPv6 addresses for the root name servers requires more than 512 bytes, which is facilitated by the EDNS0 extension to the DNS standard.
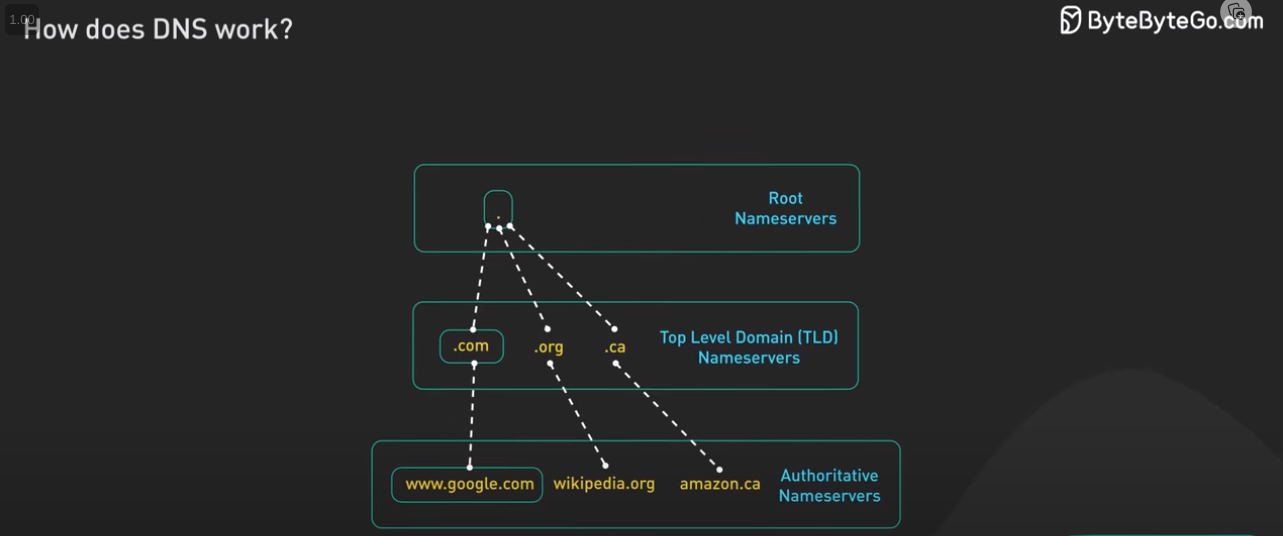
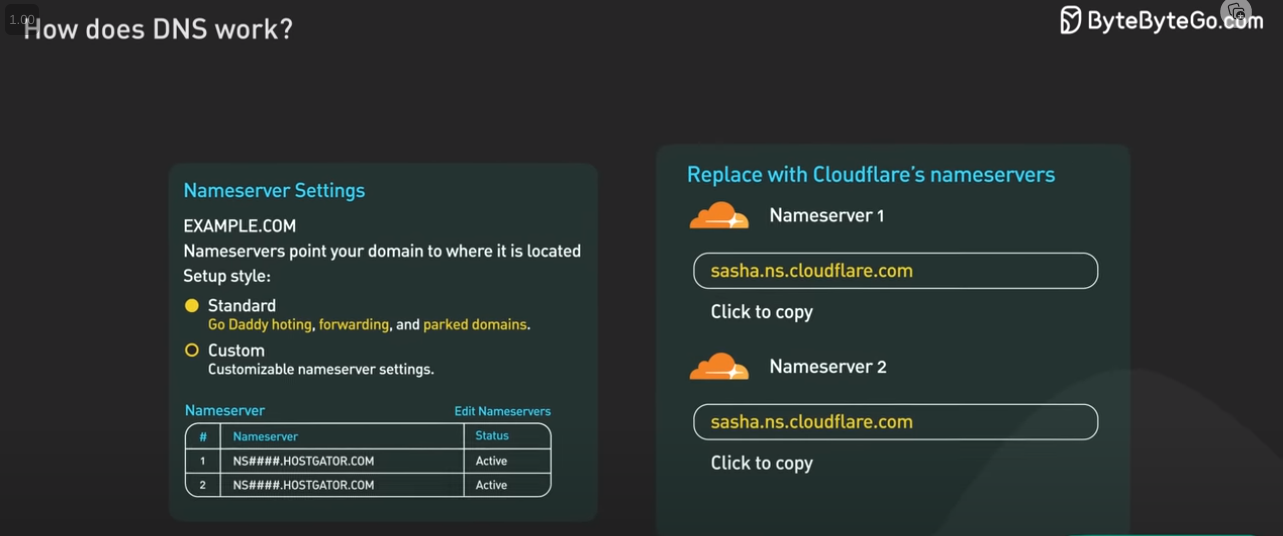
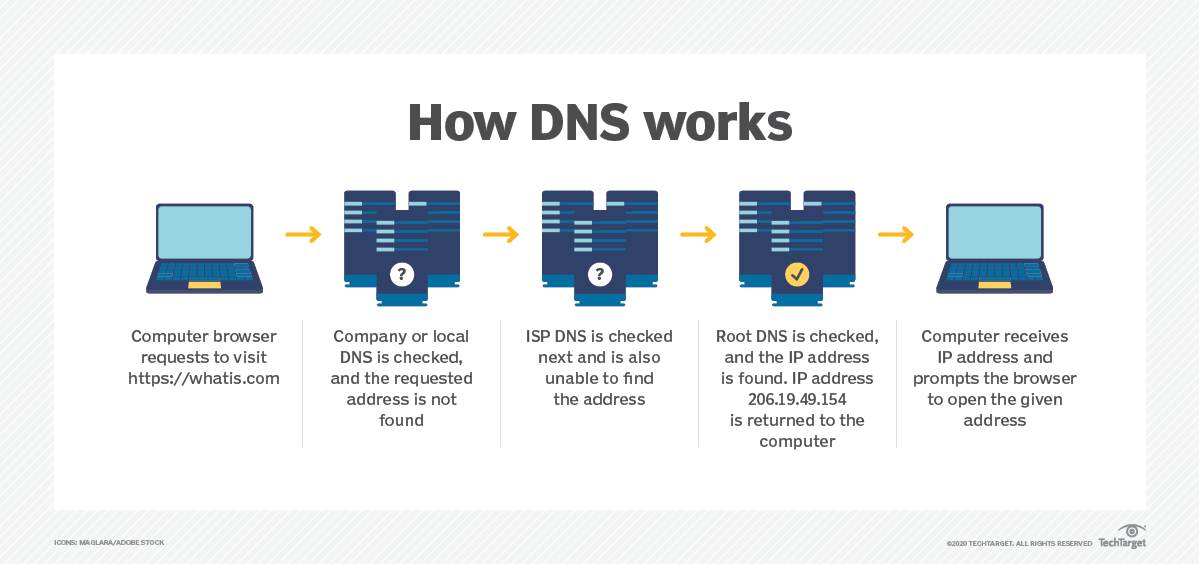
Types of DNS Servers
- Recursive server
- Root name server
- TLD serve
- Authoritative name server
Reference : types of dns servers
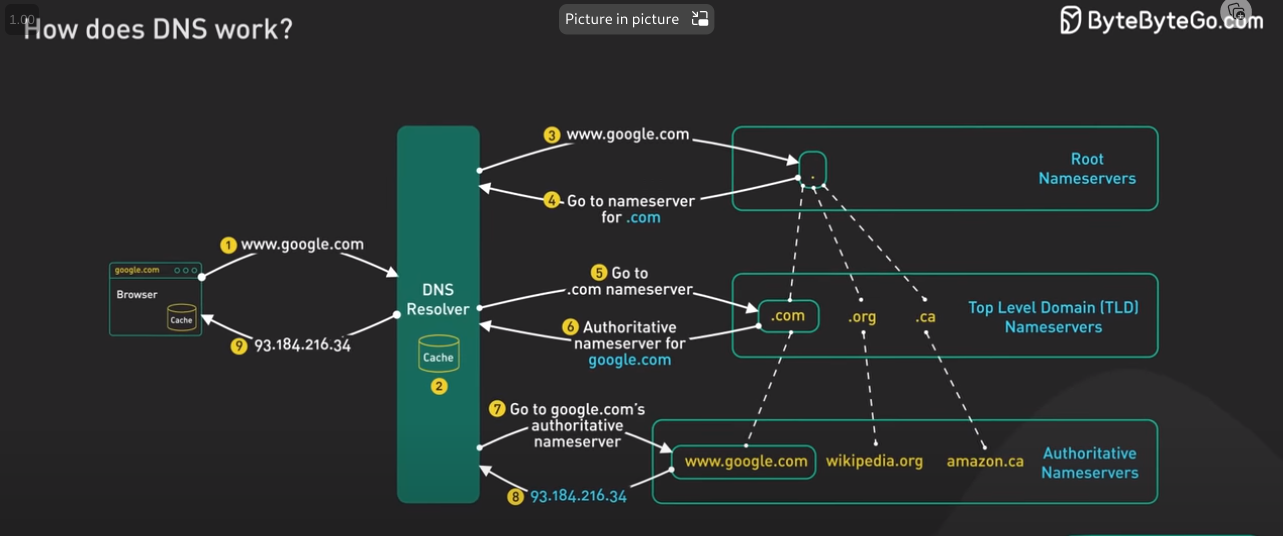
DNS Query Flow
The diagram below illustrates how DNS lookup works under the hood:
- harshityadav.in is typed into the browser, and the browser sends the domain name to the DNS resolver.
- The resolver queries a DNS root name server.
- The root server responds to the resolver with the address of a TLD DNS server. In this case, it is .in.
- The resolver then makes a request to the .in TLD.
- The TLD server responds with the IP address of the domain’s name server, harshityadav.in (authoritative name server).
- The DNS resolver sends a query to the domain’s nameserver.
- The IP address for harshityadav.in is then returned to the resolver from the nameserver.
- The DNS resolver responds to the web browser with the IP address (142.251.46.238) of the domain requested initially.
DNS lookups on average take between 20-120 milliseconds to complete (according to YSlow).
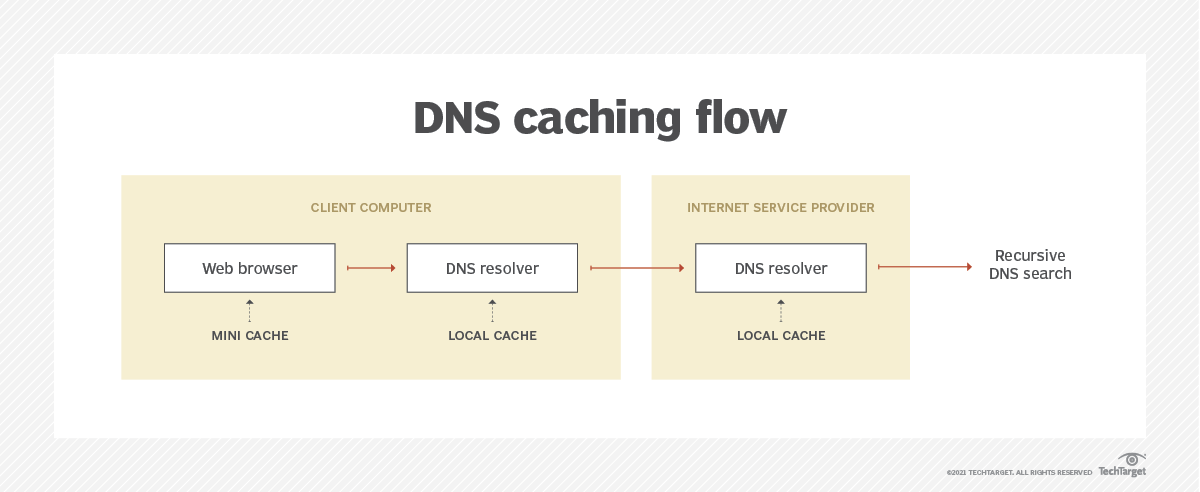
DNS Caching
DNS by Cloud Providers
- Azure : Azure DNS » Azure Private DNS » Azure DNS Private Resolver
- Google: Cloud DNS
- Amazon: Amazon Route 53
DNS over HTTPS (DOH) :
- DNS maps a domain name to an IP address, which is done by sending a UDP packet to the DNS resolver on port 53
- The data is sent un-encrypted and ISP can snoop in
- DNS over HTTPS establishes a TLS connection with a DNS resolver to stop anyone from tracking
- DNS resolved have to decrypt to read the data hence ISP can monitor
Solution: Oblivious HTTPS over DNS ODOH
- It adds a proxy layer in the middle so that the client interacts with proxy layer and the entire process is encrypted end to end
Recap
Video Reference
Reference :
- https://www.cloudflare.com/learning/dns/glossary/dns-root-server/#:~:text=A common misconception is that,addresses in the root zone.
- https://www.lifewire.com/dns-root-name-servers-3971336
- https://www.icann.org/en/blogs/details/there-are-not-13-root-servers-15-11-2007-en
- https://en.wikipedia.org/wiki/Root_name_server
- https://www.iana.org/domains/root/servers
- https://www.lifewire.com/what-is-a-dns-server-2625854
- https://blog.bytebytego.com/p/how-does-the-domain-name-system-dns
This post is licensed under CC BY 4.0 by the author.